Featured Posts
 Halo Engagement Rings Australia: Smart Diamond Choices
Halo Engagement Rings Australia: Smart Diamond Choices Round Engagement Rings UK Guide for Smart Buyers
Round Engagement Rings UK Guide for Smart Buyers Oval Lab Grown Diamond Engagement Ring Guide
Oval Lab Grown Diamond Engagement Ring Guide IT Services & Solutions for Tampa, Florida: Building a Resilient Technology Foundation
IT Services & Solutions for Tampa, Florida: Building a Resilient Technology Foundation Ready to Buy Engagement Rings with Lab Diamonds
Ready to Buy Engagement Rings with Lab Diamonds The Modern Love Story of a Custom Ring Made with Lab Diamonds
The Modern Love Story of a Custom Ring Made with Lab Diamonds Rose Gold Engagement Rings: A Timeless Choice with Modern Appeal
Rose Gold Engagement Rings: A Timeless Choice with Modern Appeal 18. The Smart Evolution of Engagement Rings You Can’t Ignore
18. The Smart Evolution of Engagement Rings You Can’t Ignore Platinum Engagement Ring Options with Lab Created Diamonds
Platinum Engagement Ring Options with Lab Created Diamonds Moissanita vs Diamante: An Honest Look from Behind the Jewellery Counter
Moissanita vs Diamante: An Honest Look from Behind the Jewellery CounterA Practical Guide to Buying Loose Lab Diamonds and Lab Made Diamonds
 Rose Gold Engagement Rings Are Stealing Hearts in Melbourne Right Now
Rose Gold Engagement Rings Are Stealing Hearts in Melbourne Right Now The Quiet Magic of White Gold Diamond Rings: Why They Still Have Our Hearts
The Quiet Magic of White Gold Diamond Rings: Why They Still Have Our HeartsBridal Jewellery Sets with Lab Grown Diamonds: Why They’re Becoming the Smart Choice
 HPHT vs CVD: The Real Talk on Lab Grown Diamonds
HPHT vs CVD: The Real Talk on Lab Grown Diamonds
Most Viewed
 How to Deal With Frozen Pipes in the House?
How to Deal With Frozen Pipes in the House? White Sapphire vs Diamond: The Sparkly Debate You Didn’t Know You Needed
White Sapphire vs Diamond: The Sparkly Debate You Didn’t Know You Needed Bitcoin Wallets: How They Work and What to Look For
Bitcoin Wallets: How They Work and What to Look For Download Mobile App Here – July Boosts Charity
Download Mobile App Here – July Boosts Charity Who Controls the Bitcoin Network?
Who Controls the Bitcoin Network? Scooter Covers Help Protect Your Mobility Scooter
Scooter Covers Help Protect Your Mobility Scooter CBD Oil for Dogs: All You Need to Know
CBD Oil for Dogs: All You Need to Know Exploring the Fifth Circuit Court of Appeals: An Insightful Guide
Exploring the Fifth Circuit Court of Appeals: An Insightful Guide Round Engagement Rings UK Guide for Smart Buyers
Round Engagement Rings UK Guide for Smart Buyers The Relationship Between Oil And Bitcoin Evolution
The Relationship Between Oil And Bitcoin Evolution 6 tips to promote your church revival event on social media
6 tips to promote your church revival event on social media Man Made Diamonds Melbourne: The Premier Choice for Ethical, Stunning Diamonds
Man Made Diamonds Melbourne: The Premier Choice for Ethical, Stunning Diamonds How to Find the Best Web Scraping App Store for Your Needs
How to Find the Best Web Scraping App Store for Your Needs 5 Core Benefits of Litigation Support
5 Core Benefits of Litigation SupportHow to Grow Your SMS Subscriber List?
Latest Posts
 Halo Engagement Rings Australia: Smart Diamond Choices
Halo Engagement Rings Australia: Smart Diamond Choices Round Engagement Rings UK Guide for Smart Buyers
Round Engagement Rings UK Guide for Smart Buyers Oval Lab Grown Diamond Engagement Ring Guide
Oval Lab Grown Diamond Engagement Ring Guide IT Services & Solutions for Tampa, Florida: Building a Resilient Technology Foundation
IT Services & Solutions for Tampa, Florida: Building a Resilient Technology Foundation Ready to Buy Engagement Rings with Lab Diamonds
Ready to Buy Engagement Rings with Lab Diamonds The Modern Love Story of a Custom Ring Made with Lab Diamonds
The Modern Love Story of a Custom Ring Made with Lab Diamonds Rose Gold Engagement Rings: A Timeless Choice with Modern Appeal
Rose Gold Engagement Rings: A Timeless Choice with Modern Appeal 18. The Smart Evolution of Engagement Rings You Can’t Ignore
18. The Smart Evolution of Engagement Rings You Can’t Ignore Platinum Engagement Ring Options with Lab Created Diamonds
Platinum Engagement Ring Options with Lab Created Diamonds Moissanita vs Diamante: An Honest Look from Behind the Jewellery Counter
Moissanita vs Diamante: An Honest Look from Behind the Jewellery CounterA Practical Guide to Buying Loose Lab Diamonds and Lab Made Diamonds
 Rose Gold Engagement Rings Are Stealing Hearts in Melbourne Right Now
Rose Gold Engagement Rings Are Stealing Hearts in Melbourne Right Now The Quiet Magic of White Gold Diamond Rings: Why They Still Have Our Hearts
The Quiet Magic of White Gold Diamond Rings: Why They Still Have Our HeartsBridal Jewellery Sets with Lab Grown Diamonds: Why They’re Becoming the Smart Choice
 HPHT vs CVD: The Real Talk on Lab Grown Diamonds
HPHT vs CVD: The Real Talk on Lab Grown Diamonds

Penetration testing is a web application security technique that is used to find vulnerabilities in web applications. The goal of a penetration test is to identify and document the web application’s flaws, as well as recommend solutions for how the web application can be improved. It’s important to note that every company has different types of web applications with varying degrees of complexity, so there isn’t one silver-bullet solution for all web app security problems. In this blog post, we’ll explore some ways you can protect your web apps from being exploited by hackers!
Why is Web Application Penetration Testing Important?
There are many web applications available on the market today. These web apps come in all shapes and sizes, which means that each web app requires a different approach to security testing. However, there are some web application features that almost every company will require:
- Authentication (login) – session management.
- Access controls (authorization) – what operations can users perform?
- Data protection (encryption/hashing) – ensuring data confidentiality & integrity during transit or at rest.
From OWASP’s point of view, Penetration testers should be able to get an idea about how easy it is to exploit vulnerabilities they find by using them against other systems. If exploits exist for common servers like Microsoft IIS, Apache Tomcat, or web application frameworks like Struts, the web app is considered to have a “high severity” risk.
The Main Goals Of Web Application Penetration Testing Are:
- Show how easy it is for attackers to find vulnerabilities in your web applications and how they can use these vulnerabilities against other systems.
- Find out whether or not there’s any malicious code that could lead to data loss or system damage.
- Improve security by finding flaws in web apps so they can be fixed before hackers exploit them!
What to Look For In A Professional Web Application Penetration Tester?
When choosing web application penetration testers, companies should make sure their web app security tests are thorough. Here are some questions you can ask web application penetration testing firms before hiring them:
- Are they familiar with the OWASP Top Ten? The OWASP community is a worldwide organization that publishes information about web application vulnerabilities to help developers build more secure applications. Having an understanding of what hackers look for when attacking web apps will give your company insight into how to improve its web app security!
- Do they have experience in other languages besides Java or .NET? Web applications nowadays aren’t just written in one language; most modern-day web apps run on multiple programming frameworks and different operating systems (Windows, Unix/Linux), so it’s important to find web application penetration testers that are familiar with the web apps you’re using.
- Do they have any certifications? Like most professional fields, penetration testing is regulated by organizations like ISC² and EC Council so it’s vital to make sure your security team has these qualifications.
The Reason Why Hiring A Qualified Web Application Penetration Tester Is Important For Web Applications:

Most hackers use automated tools instead of manually hacking into systems because manual techniques require too much time and effort! So if companies want their web apps tested thoroughly, then it’s best to hire an experienced firm that knows how attackers think in order to create tests that will truly protect its system from being exploited. A gray box penetration testing is a sort of penetration testing in which pentesters have only a rudimentary understanding of the network and infrastructure of the system under examination. The pentesters then use their knowledge of the system to perform a better job of detecting and reporting vulnerabilities.
Tools You Can Use To Help With Security And Vulnerability Assessments Of Your Website:
- Web-app scanning tools like Astra Security & Acunetix.
- Web application vulnerability scanners such as Astra Security, Burp Suite, and OWASP ZAP (Zed Attack Proxy).
- Web security testing tools like WebInspect by HP Fortify or Application Security’s AppScan Standard/Pro.
Penetration testers can use these automated web apps to help them find vulnerabilities: – OpenVas, Wapiti, Vega, and Arachni. These tools will not only look for known web app bugs but also expose any new ones that hackers may have found so companies don’t lose valuable data!
The most important thing you should remember when it comes to web application penetration testing is this: just because your company has web apps doesn’t mean it’s safe from web app attacks! Hackers are always coming up with new ways to exploit web applications, so make sure your company utilizes web application penetration testing services before you or one of its customers falls victim.
A GCP penetration testing will assist you in identifying and comprehending the security weaknesses of your GCP Cloud implementation, hence enhancing GCP security. As a consequence of this test, you will have a full and detailed understanding of the security of your Cloud deployment and will be able to take the required actions to address the concerns that have been detected.
Conclusion:
If any individual or a company wants to protect the web application, it’s essential to understand how people think and test for vulnerabilities accordingly. By taking a scientific approach to penetration testing, it can prevent attacks on your company’s digital assets by applying the right tools at the right time in order to identify potential flaws before they cause major damage.
Written by Cheryl Waller
Trending Posts
 Social Media Marketing for E-Commerce: A Comprehensive Guide to Boosting Your Online Sales
Social Media Marketing for E-Commerce: A Comprehensive Guide to Boosting Your Online Sales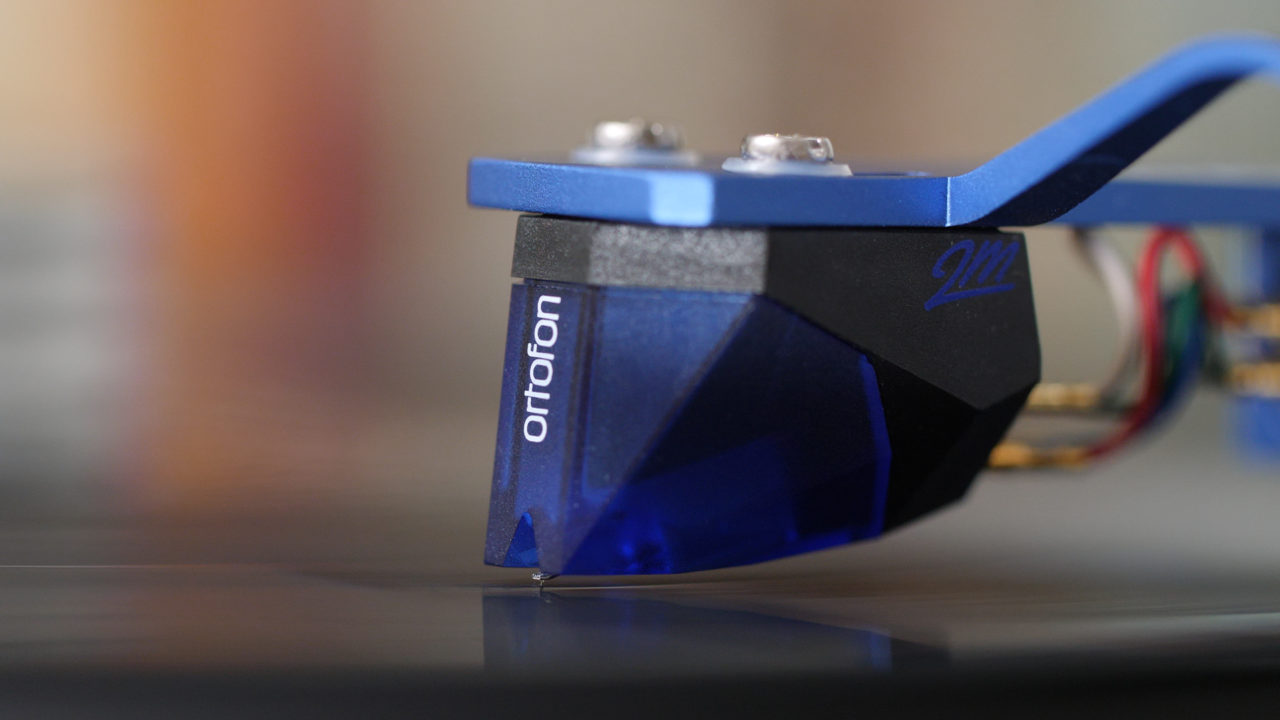 Choosing The Best Turntable Stylus For Your Budget
Choosing The Best Turntable Stylus For Your Budget Are Disadvantages Of Hiring Third Party Logistic Check Services Article?
Are Disadvantages Of Hiring Third Party Logistic Check Services Article? The Contrast Among Normal and Man Made Diamonds: An Exhaustive Aide
The Contrast Among Normal and Man Made Diamonds: An Exhaustive Aide Games That Teach You About The Stock Market
Games That Teach You About The Stock Market 8 Steps to Establish Organizational Safety Program
8 Steps to Establish Organizational Safety Program Rose Gold Engagement Rings Are Stealing Hearts in Melbourne Right Now
Rose Gold Engagement Rings Are Stealing Hearts in Melbourne Right Now Lab Grown Diamonds: The #1 Choice for Modern Jewelry Enthusiasts
Lab Grown Diamonds: The #1 Choice for Modern Jewelry Enthusiasts How to Clean Your Custom Sun Shade Sails?
How to Clean Your Custom Sun Shade Sails? Scooter Covers Help Protect Your Mobility Scooter
Scooter Covers Help Protect Your Mobility Scooter Efficient Services To Write a Research Paper as an Expert
Efficient Services To Write a Research Paper as an Expert How To Make Chicken Masala in A Steel Kadai?
How To Make Chicken Masala in A Steel Kadai? Top 10 Reasons Bitcoin is Better Than Any Other Cryptocurrency
Top 10 Reasons Bitcoin is Better Than Any Other Cryptocurrency The Pros of Java Development
The Pros of Java Development Get More from Solar Panels with These Tips
Get More from Solar Panels with These Tips
Most Viewed
 The Creation of the AI Girlfriend: Analyzing the Fun World of Artificial Assistance
The Creation of the AI Girlfriend: Analyzing the Fun World of Artificial Assistance Diamonds UK Wholesale: The Future of Sustainable Luxury
Diamonds UK Wholesale: The Future of Sustainable Luxury What Is Biticodes And How It Can Help You Trading Cryptos?
What Is Biticodes And How It Can Help You Trading Cryptos? Find The Error [pii_email_6e8e157c1031f0c4b55e]
Find The Error [pii_email_6e8e157c1031f0c4b55e] Garden Flags: Ways To Maintain And Keep Them Intact
Garden Flags: Ways To Maintain And Keep Them Intact![How To HOW TO SOLVE THE [PII_EMAIL_F471D3EE8613F77BD6E2] ERROR CODE – [GUIDE] 2021 How To HOW TO SOLVE THE [PII_EMAIL_F471D3EE8613F77BD6E2] ERROR CODE – [GUIDE] 2021](https://www.terribleanalogies.com/wp-content/uploads/2021/07/How-To-FIX-PII_EMAIL_A09AE663ED64D4128110-ERROR-CODE-IN-MICROSOFT-OUTLOOK-2021-144x144.jpg) How To HOW TO SOLVE THE [PII_EMAIL_F471D3EE8613F77BD6E2] ERROR CODE – [GUIDE] 2021
How To HOW TO SOLVE THE [PII_EMAIL_F471D3EE8613F77BD6E2] ERROR CODE – [GUIDE] 2021 How to Spot Bullish Patterns in Crypto
How to Spot Bullish Patterns in Crypto 5 Core Benefits of Litigation Support
5 Core Benefits of Litigation Support How And What Will Be The Role Of Software For Testing API
How And What Will Be The Role Of Software For Testing API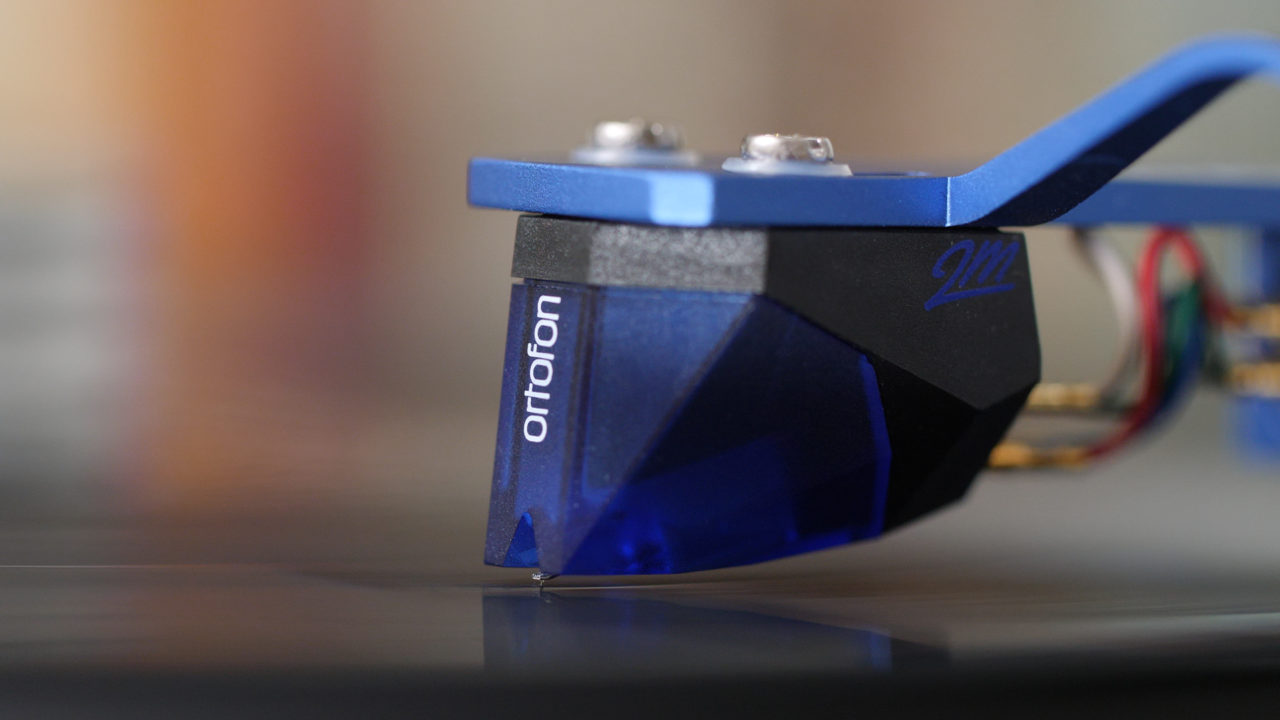 Choosing The Best Turntable Stylus For Your Budget
Choosing The Best Turntable Stylus For Your BudgetThe Ultimate Guide to Lab Diamonds CVD: A Revolution in Gemstone Industry
 Ogle pixelbook 12in Most Globally Useable Chromebook Model Of Time
Ogle pixelbook 12in Most Globally Useable Chromebook Model Of Time 6 tips to promote your church revival event on social media
6 tips to promote your church revival event on social media HPHT vs CVD: The Real Talk on Lab Grown Diamonds
HPHT vs CVD: The Real Talk on Lab Grown Diamonds Where to Sell Jewellery in Perth: Finding the Right Gold Buyers Without the Stress
Where to Sell Jewellery in Perth: Finding the Right Gold Buyers Without the Stress
Trending Posts
 Halo Engagement Rings Australia: Smart Diamond Choices
Halo Engagement Rings Australia: Smart Diamond Choices Round Engagement Rings UK Guide for Smart Buyers
Round Engagement Rings UK Guide for Smart Buyers Oval Lab Grown Diamond Engagement Ring Guide
Oval Lab Grown Diamond Engagement Ring Guide IT Services & Solutions for Tampa, Florida: Building a Resilient Technology Foundation
IT Services & Solutions for Tampa, Florida: Building a Resilient Technology Foundation Ready to Buy Engagement Rings with Lab Diamonds
Ready to Buy Engagement Rings with Lab Diamonds The Modern Love Story of a Custom Ring Made with Lab Diamonds
The Modern Love Story of a Custom Ring Made with Lab Diamonds Rose Gold Engagement Rings: A Timeless Choice with Modern Appeal
Rose Gold Engagement Rings: A Timeless Choice with Modern Appeal 18. The Smart Evolution of Engagement Rings You Can’t Ignore
18. The Smart Evolution of Engagement Rings You Can’t Ignore Platinum Engagement Ring Options with Lab Created Diamonds
Platinum Engagement Ring Options with Lab Created Diamonds Moissanita vs Diamante: An Honest Look from Behind the Jewellery Counter
Moissanita vs Diamante: An Honest Look from Behind the Jewellery CounterA Practical Guide to Buying Loose Lab Diamonds and Lab Made Diamonds
 Rose Gold Engagement Rings Are Stealing Hearts in Melbourne Right Now
Rose Gold Engagement Rings Are Stealing Hearts in Melbourne Right Now The Quiet Magic of White Gold Diamond Rings: Why They Still Have Our Hearts
The Quiet Magic of White Gold Diamond Rings: Why They Still Have Our HeartsBridal Jewellery Sets with Lab Grown Diamonds: Why They’re Becoming the Smart Choice
 HPHT vs CVD: The Real Talk on Lab Grown Diamonds
HPHT vs CVD: The Real Talk on Lab Grown Diamonds
Popular Posts
 Halo Engagement Rings Australia: Smart Diamond Choices
Halo Engagement Rings Australia: Smart Diamond Choices Round Engagement Rings UK Guide for Smart Buyers
Round Engagement Rings UK Guide for Smart Buyers Oval Lab Grown Diamond Engagement Ring Guide
Oval Lab Grown Diamond Engagement Ring Guide IT Services & Solutions for Tampa, Florida: Building a Resilient Technology Foundation
IT Services & Solutions for Tampa, Florida: Building a Resilient Technology Foundation Ready to Buy Engagement Rings with Lab Diamonds
Ready to Buy Engagement Rings with Lab Diamonds The Modern Love Story of a Custom Ring Made with Lab Diamonds
The Modern Love Story of a Custom Ring Made with Lab Diamonds Rose Gold Engagement Rings: A Timeless Choice with Modern Appeal
Rose Gold Engagement Rings: A Timeless Choice with Modern Appeal 18. The Smart Evolution of Engagement Rings You Can’t Ignore
18. The Smart Evolution of Engagement Rings You Can’t Ignore


